Take Back Your Safety in Web3: Web3 Antivirus
As the Web3 ecosystem continues to expand and revolutionize various industries, the need for robust security measures becomes paramount. Web3 technologies, powered by the blockchain and smart contracts, introduce exciting possibilities while also attracting the attention of malicious actors.
According to Ethereum.Stackexchange, popular scams may include:
-
Scam Tokens Dropped to Your Wallet Leading to Phishing Sites;
-
Reclaim Crypto Scams That Claim to Get Your Scammed Money Back, After You Have Been Scammed Once;
-
Password Recovery & Private Key Recovery Scams That Claim to Restore the Access to Your Account or Wallet.
These are so-called authorised transfer scams. As opposite to the hacks, the users voluntarily transfer away their money with their our authorisation. Outside scams, there exist other cybercrime that may cause you to lose your assets:
-
Fake Airdrops;
-
Fake NFT mints & Claim scam;
-
Malware esp. on Microsoft Windows desktop computers directly extracts the private key from the wallet;
-
Your computer gets infected with a malware when you install pirated software or random EXE files from Internet.
-
Honeypot via: twitter.com/lordnarfz0g/status/1554649309580300288 CDN NFT honeypot (Canarytokens and Iplogger), or other honeypots.
Clipper Attack Illustrated:

In short, crypto clipper, address poisoning and «zero-transfer/approve transaction» attacks are just vanity-generated address attack variations! For example, that’s how scammers are using vanity-gen to generate an address similar to the victim’s ones (first 4 and last 5 digits are similar) in a address poisoning attack. This is common at ETH, BSC, even BTC!
Web3 Antivirus: Attacks & Protections
To ensure a safe and secure Web3 environment, Web3 Antivirus emerges as a critical player, offering comprehensive protection against a range of emerging Web3 attacks. In this article, we will explore several significant attacks that Web3 Antivirus can safeguard Web3 users against!
First and foremost, I want to sincerely thank the authors of all the resource materials for their assistance, as they have been invaluable in providing me with much-needed information and removing the veil of secrecy!
https://web3antivirus.io/?source=post_page-----ed839f7d204e--------------------------------
I also strongly advise that you read the list of resources and research for self-study that you will find separately in order to improve your comprehension. Therefore, below you will see not a typical article, but a Systematization of Knowledge — SoK, in which I will rely on Authors that I myself trust in this matter. Let’s get started!
Guarding the Web3: Protecting Users from Emerging Web3 Attacks
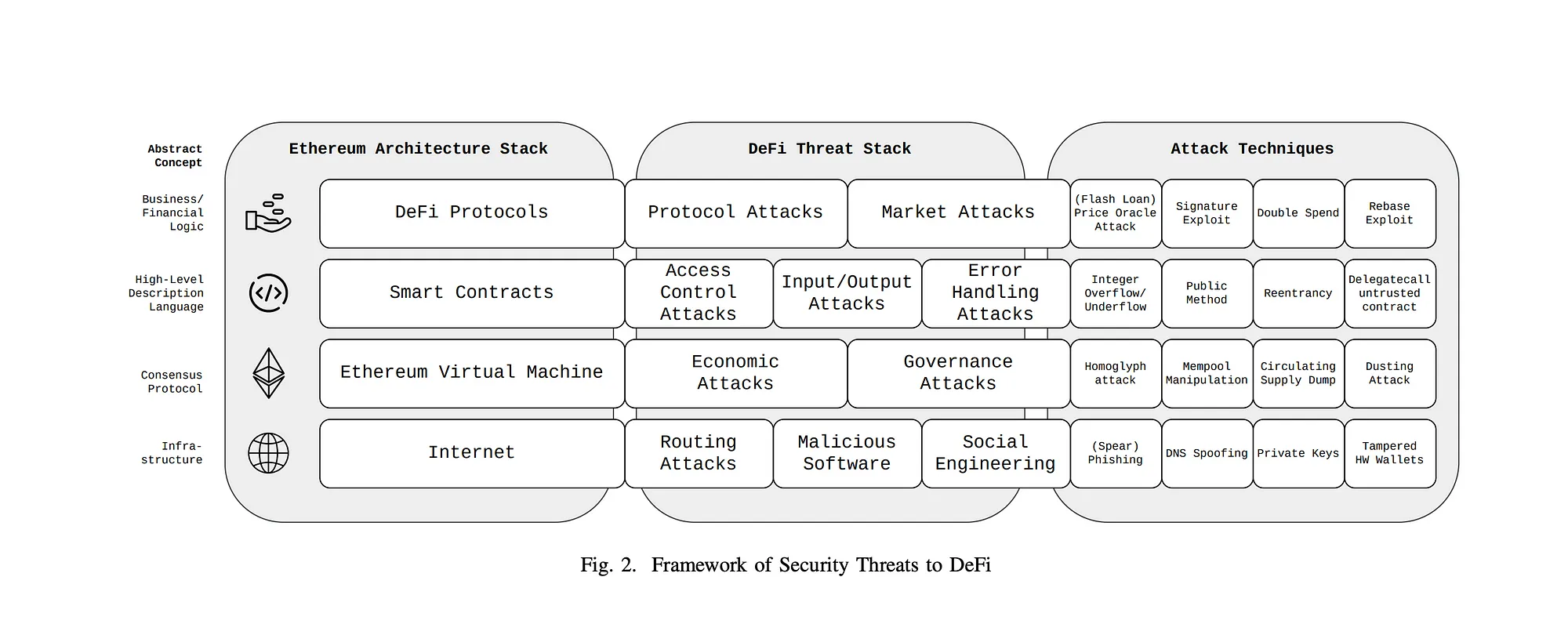
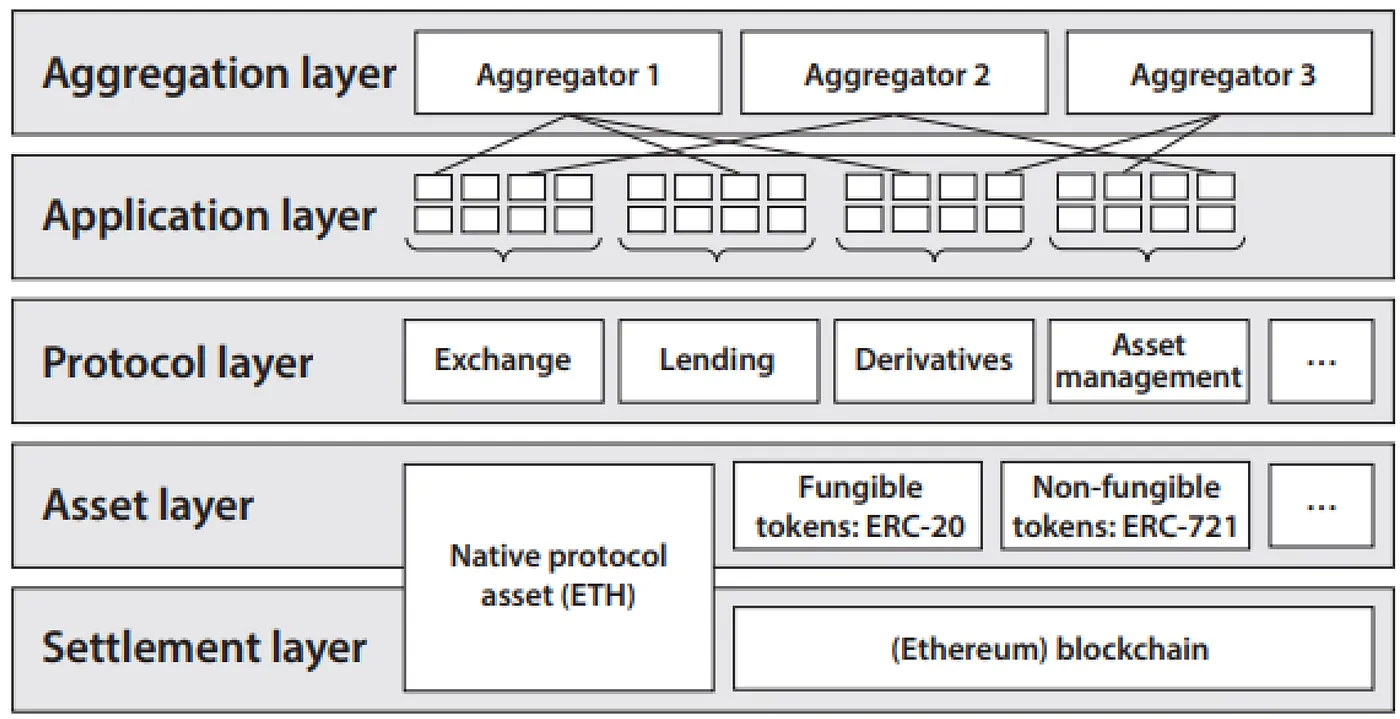
Web3, short for Web 3.0, refers to the internet’s next generation that incorporates decentralized technologies like blockchain, smart contracts, and distributed ledger systems. While Web3 brings numerous benefits such as increased transparency, immutability, and decentralization, it also introduces new security challenges.
According to Chainanalysis, while the first half of 2023 saw a reduction in crypto scam revenue by nearly $3.3 billion compared to 2022, totaling just over $1.0 billion, ransomware remained a persistent issue. With it, crypto hackers adapting their strategies as crypto theft decreases by two-thirds in 2023.
To address these security challenges, it is essential to integrate antivirus solutions specifically designed for Web3 applications. By integrating antivirus solutions into Web3 applications, developers and users can benefit in several ways:
-
Enhanced Security: Antivirus solutions help identify and mitigate security vulnerabilities, preventing potential exploits and attacks. Regular audits and analysis of smart contracts, dependencies, and oracles contribute to a more secure Web3 ecosystem.
-
Increased Trust and Confidence: Antivirus solutions instill trust and confidence among users and developers, as they know that their assets and transactions are protected by robust security measures. This increased trust can drive adoption and the continued growth of Web3 applications.
-
Reduction in Financial Losses: By minimizing the risks associated with security vulnerabilities, antivirus solutions offer protection against financial losses. Prevention of supply chain attacks, oracle manipulation, and phishing attempts can save users and developers from significant monetary damages.
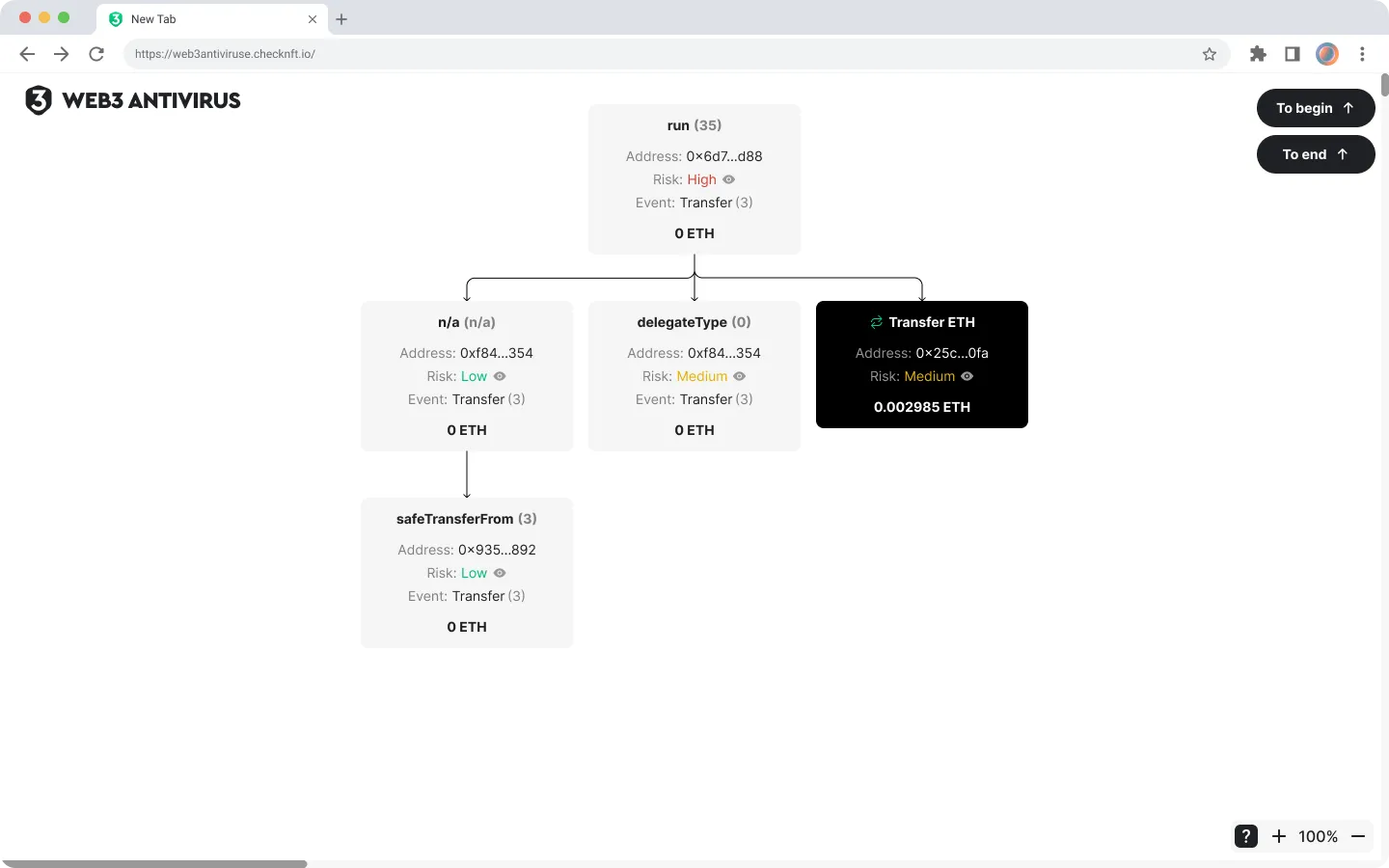
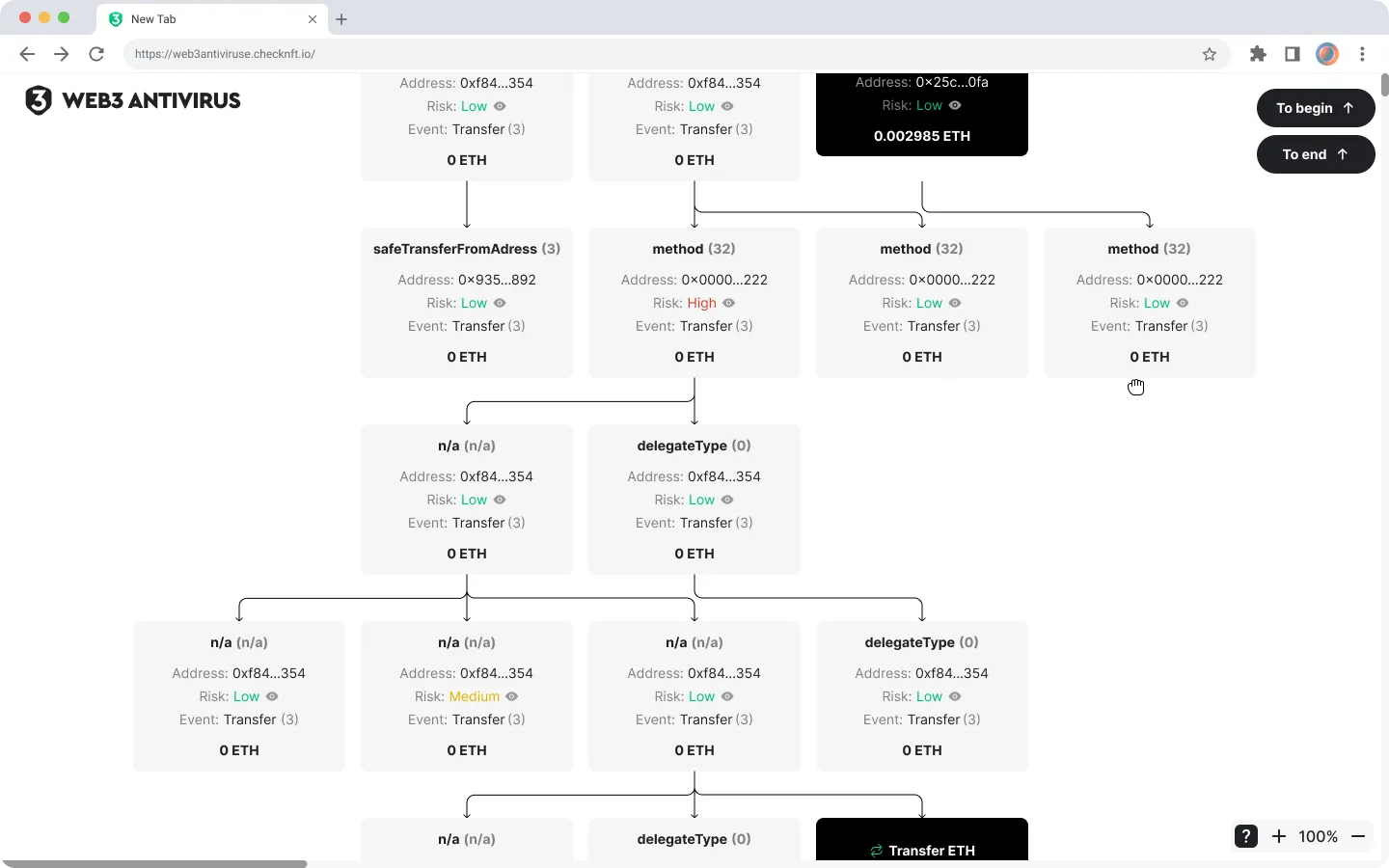
In short, it comes from eth_sign, transfer_from functions & eip-712 making theft possible as they don’t respect any allowances. One solution is to use a special app which will simulate a transaction right before you interact with a smart contract.
But there is also an important thing to keep in mind! An important part about this is was this caused a rally around “tx simulation for safety”, but simulation may introduce a new vector for impersonating a credible looking claim.
Even though some attack vectors are possible, the pros of these services obviously outweigh their disadvantages and allow you to significantly reduce the damage to your community through hundreds of “low-level” attacks.
Web3 applications hold enormous potential in revolutionizing various industries by leveraging decentralized technologies like blockchain and smart contracts. However, the security challenges associated with this emerging ecosystem cannot be ignored. Integrating antivirus solutions tailored specifically for Web3 can significantly enhance the security and trust of these applications.
By conducting smart contract audits, analyzing third-party dependencies, preventing phishing attacks, and verifying oracles, developers and users can confidently engage with Web3 applications, driving their adoption and ensuring a secure future for the decentralized web. To ensure a safe and secure Web3 environment, Web3 Antivirus emerges as a critical player, offering comprehensive protection against a range of emerging Web3 attacks!
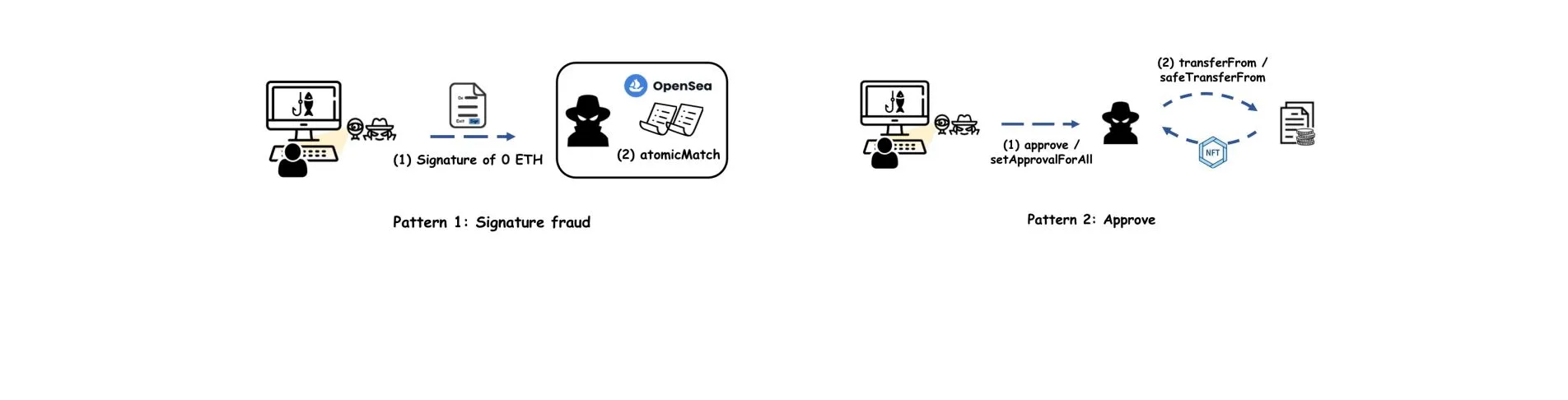
Signature: Hidden Danger
Today we will also deal with what we in our arthouse understanding of the web3 security is called the “blue button of death” and then Ortomich will talk about this type of attack using the signature function, which uses EIP-712 — in our subjective opinion, very underestimated danger!
At first, I would like you to study this resource to get an understanding of the issue before reading article:
Do not confuse it with allowance approve scam which targets ERC20 tokens, but not Ethers. (1, 2, 3, 4). With it, a malicious signed approval can be blocked if you front-run (part of MEV) the attacker calling permit with your own same-nonce signed approval!
Approve Button Threat
A lot of tokens on Ethereum use the ERC/EIP20 standard. This is a standard interface for the token contract that details the contract properties, functions, function arguments, and function return types.
One of these standard functions is function approve(address _spender, uint256 _value) public returns (bool success). This allows a third-party to send tokens from your account on your behalf. You’ll recognize this pattern if you’ve ever done a swap through an AMM (like Uniswap) as you’ll have to approve the AMM to spend your tokens before you swap.
Bad actors have learned how to exploit this function, as it’s harder for unsuspecting users to avoid when they’re only expecting scams that outright ask for their private keys.
Exploiting token approvals is a clever approach because users generally think: “If they don’t have my key, then they can’t sign a transaction, so they cannot steal my assets.” Whilst generally accurate, this is not true when we talk about ERC20 tokens and other token standards.
If you or someone you know may have approved unnecessary amounts of tokens on any product, fix it now with revoke.cash or app.unrekt.net !
EIP-712: PoC
First, a little preface. This EIP allows you to approve tokens by signing, that is, if you are already used to all approves being given as a separate transaction, you won’t believe it, you can also approve with a simple signature, which will save you some gas.
This EIP is implemented in some ERC20 tokens, among them $USDC, $UNI and others. Everybody got used to the fact that the signature does not carry any danger, but then we showed you how you can steal all the money from your wallet with eth_sign function:
But that method had one special feature — a big red warning sign from the wallet that warned you about the risks. In this case, if an attacker forges a signature for EIP-712, the wallet will probably not warn you in any way and you will not even know that you have been scammed!
To understand the next paragraph, you need to learn for yourself how signatures work and have an idea of the structure of a smart contract.
Next, we need to make that very signature. The EIP-712 type can differ from token to token, so ideally you should look for a different signature approach for each token.
Then we have to take v, r, and s from our signature and pass them and a few other parameters to the permit function on the token contract we want to access.
As we can see, at the very end of the function, after all the checks have been passed, we see a call to the allowance function, which is responsible for approving.
If it’s a signed approval (ERC-2612), the chain id is embedded so it only works on a specific chain, and there’s a nonce to prevent replays! But you cannot un-sign a eip712 scam sign, so signed once = lost an address!
You must keep in mind that DAI actually predates the 2612 standard but does include nonce!
With all said, a malicious signed approval can be blocked if you front-run the attacker calling permit with your own same-nonce signed approval. But not all eip712 implementations include a nonce.
Some thoughts on a security compromise related to EIP-712 made by InstaDapp for their Avocado multi-chain experience!
It isn’t part of the 712 standard but of the permit standards like ERC-2612! If it’s a signed approval (ERC-2612), the chain id is embedded so it only works on a specific chain, and there’s a nonce to prevent replays. Present article included DAI, which does. DAI actually predates the 2610 standard but does include nonce.
Final Thoughts: Use Web3 Antivirus
That said, it doesn’t really matter what industry you’re in. If you have any sensitive, proprietary information at all, then you could very well be a target. This is a good thing to always keep in mind.
Learn the latest attack techniques, white-hat cheatsheets and defense methods, join hacker communities — because only with knowledge can we defeat the knowledge of hackers. In this intellectual battle the most prepared will win and I believe that it will be you, Anon.
It sounds scary but it is possible, the main thing is to always think ahead!
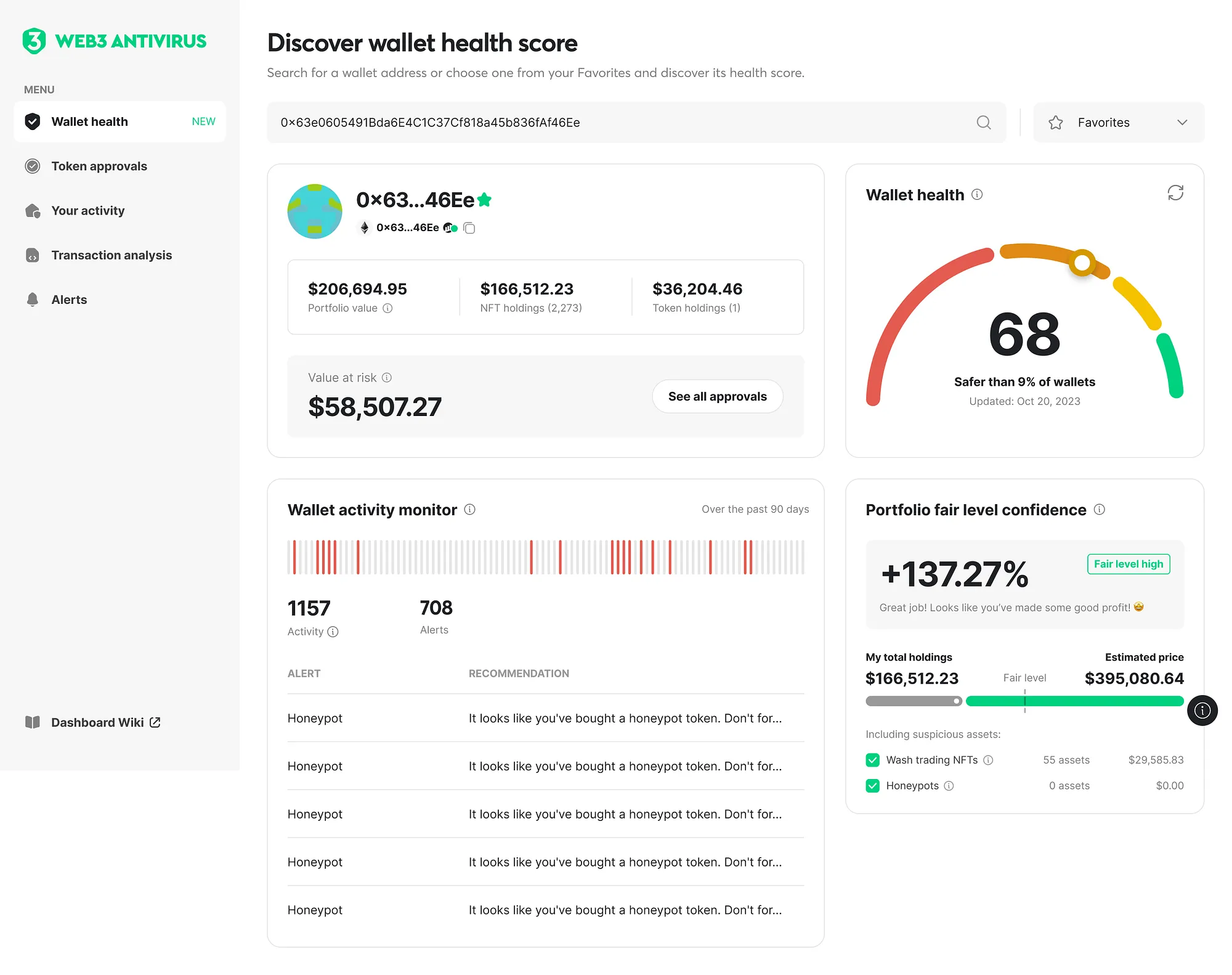
As the Web3 ecosystem continues to evolve, the need for comprehensive security measures becomes increasingly vital. Web3 Antivirus emerges as a powerful solution, proficiently shielding Web3 users from a wide range of emerging attacks.
Through its cutting-edge analysis techniques, continuous monitoring, and proactive protection mechanisms, Web3 Antivirus raises the security bar within the Web3 ecosystem. Try Web3 Antivirus, a cutting-edge solution designed to safeguard users from a wide range of attacks that threaten the integrity and security of their transactions and interactions with the decentralized web!
This section delves into the innovative features and capabilities of Web3 Antivirus, shedding light on its efficacy in defending against various cyber threats encountered within the web3 ecosystem:
-
Anti-Phishing Protection: Utilizing AI and machine learning algorithms, Web3Antivirus.io detects phishing attempts and warns users to prevent compromising their private keys or personal information.
-
Real-time Threat Monitoring: The platform constantly monitors the blockchain network, identifying suspicious activities and notifying users promptly, allowing them to take immediate action.
-
Secure Wallet Integration: Web3Antivirus.io supports seamless integration with a range of popular wallets, offering enhanced protection against unauthorized access and ensuring a secure storage environment for digital assets.
-
Transparent Decentralized Protection: By using decentralized infrastructure, the platform ensures transparency, security, and immutability, reducing the risk of data tampering or manipulation.
-
Community-Driven Security: Web3Antivirus.io fosters a collaborative environment, allowing users to report vulnerabilities and contribute to the overall security of the web3 ecosystem.
By mitigating vulnerabilities, detecting malicious behaviors, and thwarting attacks, it establishes a secure foundation for the future of Web3, inspiring user confidence and promoting the widespread adoption of transformative technologies.

Web3 Antivirus stands out as a leading solution in the web3 security landscape. By addressing critical security challenges faced by web3 users, from phishing attempts to smart contract exploitations, the platform provides an all-encompassing security shield.
With its innovative features, continuous threat monitoring, and collaborative community-focused approach, Web3 Antivirus ensures the integrity, privacy, and peace of mind for users navigating the decentralized web.